For those who are new to the subject, rooting Android, or doing so-called root, is essentially getting high permissions. With root access, you are able to access and modify files that would normally be inaccessible, such as those stored in the /data and /system directories.
Having root access also allows you to run an entirely different class of third-party applications that perform deep system-level modifications. You will also be able to access certain features which were inaccessible or use existing features in new ways.
However, getting root access is not the end of the whole process of modifying the device – on the contrary, it is usually the first step on your journey to modifying Android. As such, root access is often used to install a custom recovery that can then be used to install custom ROMs, kernels, and other system modifications.
Root access also allows users to install the powerful and versatile Xposed Framework, which acts as a “bridge” between the system and the upper layers of Android and allows you to perform operations without any modification to the internal OS files. It is even possible to correct any system bugs. Due to its inherent power, having root access is often dangerous.
Fortunately, releasing root is not leaving the system open for everything; and to correct the “hole” left in the SO, there are programs such as SuperSU or SuperUser, which only grant root access to applications of your choice. It works like this: when you run an app that needs root permission, a popup window will ask whether you allow or not allow the operation. As a result, system security is not compromised.
In cases of disaster, having root can save you a lot of time. There are several backup utilities that work with root permissions to help you restore applications and settings exactly as they were before. An example is the Titanium Backup program. There is even the possibility of performing a full backup of the entire OS through recovery, allowing you to return the operating system exactly as it was at the time you created the backup.
In addition to the obvious advantages of keeping your system backed up or only the applications and settings, there is a whole range of software for a variety of purposes that will give you greater control over your device and the programs running on it.
Finally, it is possible to stay forever writing about the virtues of root access, so let’s show you how to carry out the process:-
A very practical method created by a developer of XDA Developers allows to carry out the process without using the computer. Just install an application and run it for the magic to happen.
1. Download Framaroot on your Android device;
2. Be sure to enable off-store application installation from Google. Go to Settings> Security and check Unknown sources;
3. Use a file manager to search for the APK you downloaded. When you find the program package, tap it to begin the installation;
4. Once the application has been installed, run it from your application drawer (App Drawer);
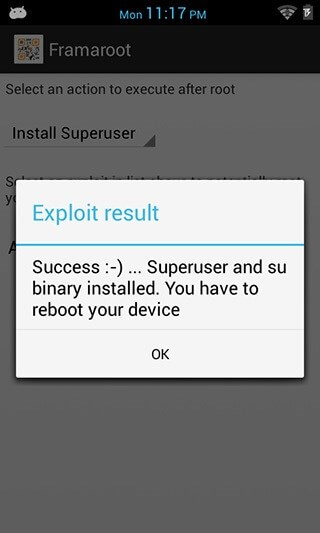
5. Select the SuperSU installation from the first drop-down menu;
6. Select the type of exploit that will be used. The program usually offers three types, but may vary by device. See below which one is most appropriate for your device;
7. After that, just wait for the process to end;
8. Then simply restart your device after the process is complete.
List of exploits used by Framaroot
- Sam (affects devices with Exynos processor);
- Frodo (affects devices with Exynos processor);
- Gimli (affects devices with Omap36XX processor);
- Merry (affects devices with Exynos processor);
- Aragorn (affects devices with Samsung processor);
- Legolas (affects devices with Samsung processor);
- Gandalf (affects devices with Qualcomm processor);
- Boromir (affects devices with MediaTek processor);
- Pippin (affects devices with K3V2 processor);
- Gollum (affects devices with AMLogic processor);
- Faramir (affects devices with MediaTek processor);
- Barahir (affects devices with MediaTek processor).
To find out what type of processor your device is, simply install the CPU-Z application by clicking here.
I couldn’t root my phone with it ….it keep telling me “Failed:-( try another exploit if available (Error 9#)
Is that we can disable the root app from android?